This post will discuss a key project document, i.e., the risk register.
Organizations initiate projects to achieve their goals. However, these projects carry risks that can affect their success, resulting in a loss of organizational resources. As a project manager, you must prepare to deal with such risks, and a project risk register is a great help here.
A risk register is an important project management document in risk management. Risks are identified at the early stage of the project, and it is a key process of the risk management plan.
You cannot avoid or eliminate all risk events, but you can manage them using risk management.
A risk register provides all information on project risks, allowing you to make informed decisions.
Risk Register
Definition: A risk register is a management tool that contains a list of identified risks to help you assess risks, plan responses, and monitor and control them. It lists prioritized risks and risk analysis, including the probability of occurrence and impact.
You can also add more details required by the project’s complexity, such as qualitative risk analysis and quantitative analysis, response plan, risk owner, and updates.
Many jurisdictions require risk registers as a transparency tool to protect the interests of investors.
A risk register provides details on project risks, allowing you to make better decisions. It delivers organized data to analyze risks rather than guessing on the fly.
It is a live document that is updated in real time.
A risk register is sometimes also known as a risk log.
What is the Purpose of a Risk Register?
A project risk register provides stakeholders with a list of potential risks, ranking, analysis, and response plans.
You can update the register if you identify new risks. The register is also updated when any risk occurs, does not occur, or changes its status, such as from high priority to low priority.
This register provides complete information on risks, including the owner and who will take action once a risk occurs.
When Should You Use a Risk Register?
You should use a risk register on all projects, regardless of size or complexity. It is an integral part of the risk management process.
A risk register can have essential information for smaller projects, such as the list of risks, ranking, the likelihood of occurrence, risk response, owner, and watch list.
A watchlist includes a list of the lowest priority risks that only require monitoring, and no risk response plan is developed for these risks.
Large and complex projects can have more details, including risk category, description, impact, probability, rating, qualitative and quantitative risk analysis, mitigation strategies, ownership, status, residual risk, etc.
Risks can be ranked by priority as follows:
- Low-level Risks: These have a low impact on your project. These risks will not likely result in failure, harm, injury, etc. However, you can keep them under the watch list for monitoring.
- Medium-level Risks: These risks can affect your project objective, and you must monitor them regularly and keep a close watch.
- Critical Risks: These are high-priority risks and can severely affect your project, so watch them closely.
A risk register can help you identify patterns and plan strategies to deal with such patterns for future projects. Therefore, it is a vital part of your organizational process assets.
Do not forget to include positive risks. You can use a risk register to take advantage of opportunities while reducing the impact of threats.
Common Risk Scenarios
A project faces many risks, including internal and external.
External risks include political conditions, supply chain, operational, IT/cybersecurity, finance, investment, security, legal, strategic, regulatory, market, natural disasters, cyber security, IP theft, etc.
Internal risks include equipment malfunction, team members leaving the team, schedule delays, cost overruns, etc.
You must be careful if your project is in a natural disaster-prone area. You cannot control these risks, and the impacts are devastating.
Miscommunication can affect projects and can cause scope creep.
If delays go unnoticed, they can affect your milestones and deadlines. Schedule delays can cause rushed deliverables and team confusion. A proper schedule helps keep the project on track and results in on-time deliveries.
In many cases, the project misses the scope. You can mitigate this risk if appropriately tracked in real time. However, you cannot track deliverables to concerned stakeholders without a proper RACI matrix. Ensure your project has one responsibility assignment matrix.
Projects with a massive inventory have a risk of theft or reporting errors. Theft causes loss of revenue, uncertainty, and misuse of time. Therefore, ensure your project materials and consumables are safe and well-recorded.
Risk Register Content
A risk register can include the following elements:
Risk Identification
- Risk Category: This is the specific risk category; it includes internal or external risks such as finance, legal, supply chain, natural disasters, operational risks, and project-specific risks. This grouping provides risk clustering, letting project managers reasonably guess these dangers.
- Risk ID: Every risk is assigned a unique identification number for tracking.
- Risk Description: This explains the risk, what it comprises, how it will affect the project objective, etc.
Risk Analysis
- Risk Impact: This shows the potential effects of the risk on the organization’s operations or the success of the project.
- Risk Probability: This is the likelihood of the risk occurring. Risk probabilities range from most likely, likely, and not likely.
- Risk Ranking: You multiply risk impact by probability and get the risk score. The higher the risk score number, the higher the ranking.
- Risk Consequence: This involves the consequences of the risk occurring.
Risk Evaluation
- Risk Scale/Exposure Rating: You get the risk exposure or rating by combining the risk probability with the impact. Risk exposure is an overall risk of a project or an organization.
- Risk Trigger: This lets you know if a risk is about to occur. Identifying triggers is crucial to stop occurring risk before it becomes an issue.
- Risk Priority: You determine the risk priority by multiplying the impact and probability values.
Risk Response Plan
These are the actions to reduce, prevent, or eliminate risk. A risk response plan comprises a plan on how to handle risk. The complexity of the response plan depends on the severity of the risk.
Risk management planning includes identifying, analyzing, planning a response, monitoring, and controlling the risk. Responses include accepting, transferring, mitigating, avoiding, and escalating.
- Contingency Plan: This plan reduces the impact or probability of the risks.
- Risk Owner: This is the person assigned to manage the risk. The risk owner manages and executes the mitigation measures against the specific assigned risk.
- Risk Status: This is the status at a particular moment. A risk’s status can be ongoing, open, or closed. Risk statuses are significant in monitoring risks, as they help determine higher-priority risks.
- Residual Risk: Even after controlling, monitoring, and managing risks, there will always be some level of risk that you cannot completely reduce. You can record such risks in this category for continued monitoring. p
- Secondary Risk: This risk is because of the response to a primary risk.
You can add two additional fields: “timeline” to show the periods when various risk register items were created and executed; and “response type,” which can be positive or negative depending on the analysis.
How to Create a Risk Register
Let’s look at an example of mitigating natural disaster risks.
Identification
Identify potential project risks and assign them their class, type, name, and identification number. It would be best to involve all project stakeholders and subject experts to collect the risks.
For example, since you are in a disaster-prone area, you should know the prevalence of storms, floods, or heat waves in your region.
Description
Describe the risk with possible impact.
For example, a flood might cause the closure of major highways, resulting in supply and delivery delays, which might impact the firm’s revenue.
Estimate the Impact
Estimate the impact of the risk.
For example, if a flood occurs, this means the closure of business facilities and a loss of revenue. Also, it can delay business plans due to the disruption of business operations.
Prioritize Risks
Once you have recorded all the risks, organizing them according to their priority is crucial. The most important has the highest priority, and the least important has the lowest.
Floods have a high priority as they can destroy the entire operation, so you should regularly monitor such a risk for its trigger and stop it from becoming an issue.
Plan Risk Responses
Developing a response plan is a crucial step. In this case, a flood can be monitored through constant weather monitoring to ensure no warning signs, such as strong winds or heavy clouds, occur during business hours.
For such a risk, avoid risk response strategy is the most appropriate strategy and involves evacuating organizational personnel out of business premises and sensitive equipment before the flood happens. Also, this reduces damage, enabling the business to resume operations much faster.
The best risk response strategy for flood is to avoid it; however, invest in insurance if it is impossible.
Determine Risk Owners
You can delegate risk management tasks to owners for better control.
The flood risk owner should ensure constant trigger monitoring, reporting, and implementing avoidance measures.
Risk Register Example
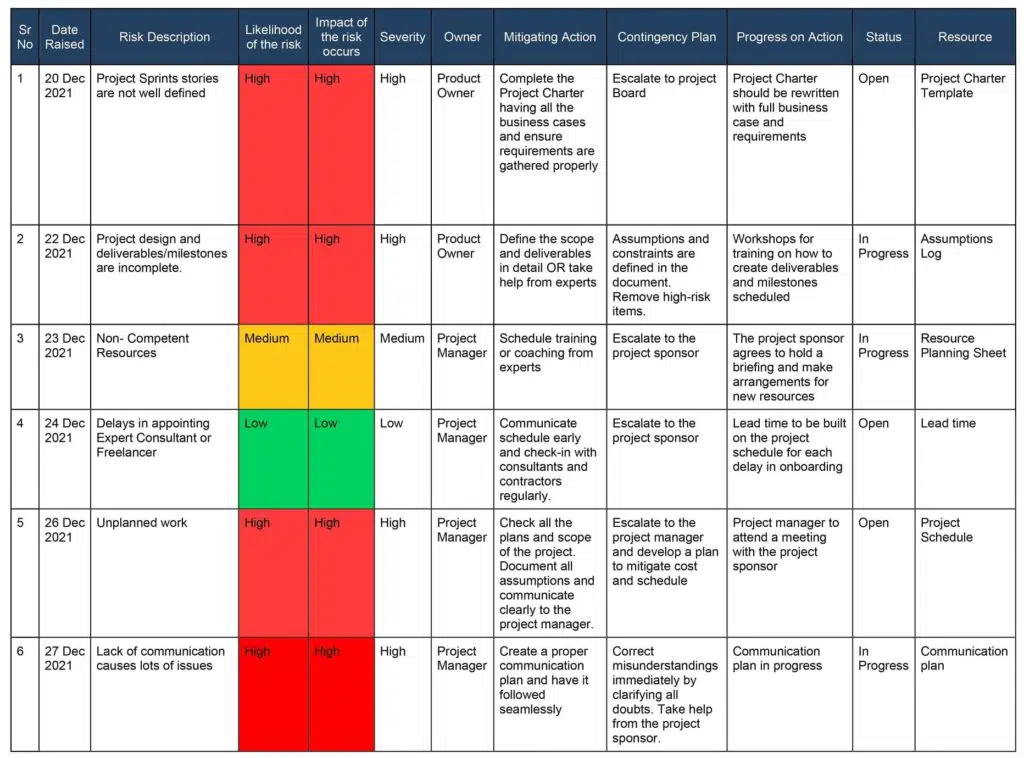
The following images show an example of a risk register.
Risk Register Example

Who Creates a Project Risk Register?
Creating a project risk register is not a one-person task. A project can have a responsible person to manage the risk register, such as a risk manager or project manager, but creating a risk register requires a combined effort.
To create a project risk register, project managers will involve team members, subject experts, management, project sponsors, etc. However, the project manager is responsible for developing the risk register.
Risk Register Vs Risk Matrix
A risk register and a risk matrix are management tools commonly used in risk management to assess and analyze risks within a project. Though they serve similar purposes, they differ in structure and the information they provide.
A risk register is a comprehensive database that records all identified risks, serves as a centralized repository of risk-related information, and provides a detailed account of each risk.
A risk register can include the following components:
- Risk Identification: Each risk is identified and given a unique identifier for easy reference.
- Risk Description: A detailed description of the risk, including its nature, potential consequences, and triggers or causes.
- Risk Owner: The person or team responsible for monitoring and managing the risk.
- Risk Impact: The potential impact of the risk on the project or organization, such as cost, schedule, quality, or reputation.
- Risk Probability: The likelihood or probability of the risk occurring.
- Risk Severity: An assessment of the overall severity of the risk, which combines the impact and probability.
- Risk Response: The strategies and actions planned or implemented to address the risk, such as mitigation, acceptance, or transfer.
- Risk Status: The current status of the risk, including its likelihood, impact, and response effectiveness.
- Risk Mitigation: The specific measures or controls in place to reduce the likelihood or impact of the risk.
- Risk Monitoring: The process for ongoing monitoring, review, and reporting of the risk.
- Risk Closure: When the risk is resolved, mitigated, or no longer relevant, it is closed in the register.
A risk matrix, also known as a risk heat map, is a visual representation of risks that helps assess their significance based on their probability and impact. It typically uses a two-dimensional grid to categorize risks into different levels of severity.
The risk matrix has the following key elements:
- Probability: The likelihood of a risk occurring, often represented along one axis of the matrix.
- Impact: The consequences or severity of a risk is represented along the other axis.
- Risk Levels: The matrix divides the intersection of probability and impact into different risk levels or zones. These levels can be color-coded or assigned numerical values to indicate the severity.
- Risk Assessment: Each identified risk is plotted on the matrix based on its estimated probability and impact. This allows for quick visualization of the relative significance of the risk.
- Risk Prioritization: The risk matrix helps prioritize risks by focusing on those falling within higher-risk levels. This guides decision-making and resource allocation for risk management efforts.
The risk register provides a more comprehensive view of individual risks, including their description, owner, impact, response, and monitoring status. It allows a thorough understanding of each risk and its management process. On the other hand, the risk matrix offers a visual representation that aids in quickly assessing and comparing risks based on their severity.
Both tools are used together. The risk register serves as the primary repository for detailed risk information, while the risk matrix offers a condensed summary that can be shared with stakeholders or used for high-level discussions.
Conclusion
A risk register is a key project document for any project. It lets you organize risk information and allows management to make better-informed decisions that influence the success of the project.
It helps identify, assess, and manage risks down to acceptable levels.
Therefore, you should start developing the risk register from day one of the projects, keep it updated throughout the project life cycle and store it in organizational process assets after completing the project as a lesson-learned document.
This topic is important from a PMP and PMI-RMP exam point of view. Therefore, understand it well.
How does the risk register help in your project? Please share your thoughts in the comments section.

I am Mohammad Fahad Usmani, B.E. PMP, PMI-RMP. I have been blogging on project management topics since 2011. To date, thousands of professionals have passed the PMP exam using my resources.